There are times when technology can create a great deal of tension challenging the status quo and effecting immediate change.
This post takes a look at the effect of encryption on law enforcement both historically and most recently with the announcement by Google and Apple Inc: to strength mobile data encryption by providing default encryption mechanisms for users of both the Android and iOS operating systems. It explores the alarming response to this announcement by American law enforcement agencies and examines whether or not there is merit in the disturbing picture painted by law enforcement of investigations being foiled by the government’s inability to decrypt communications.
I. Introduction
The CIA triangle represents the foundational goals of Information Security: Confidentiality, Integrity and Availability; Cryptography is used to primarily provide the first of this triad – Confidentiality. Cryptography involves the use of ciphers (encryption algorithms) to encipher and decipher messages so that only the intended recipient is able to gain access to the encrypted message. In practice, cryptography is susceptible to many types of attacks however modern cryptographic methods have evolved from Caesar and Vigenère ciphers to algorithms which are extremely difficult to break. Today’s “strong encryption” requires the use of super computational power to crack and even then the amount of time needed to break these ciphers, often make the job unthinkable and unachievable in this lifetime; this presents a challenge to law enforcement organizations.
This post is structured as follows: section II briefly describes the encryption methods used by Apple’s IOS and Google’s Android operating systems, the two market leaders in the mobile operating system market. It also highlights the changes, to mobile data encryption announced by both vendors in 2014 and the concerns which resulted in regard to law enforcement. Section III sheds some light on the history of law enforcement and strong encryption, detailing some of the measures taken historically by the US Government to assist law enforcement agents with the challenges of encryption technology. Section IV provides an analysis of both sides of the strong encryption debate and highlights some possible strategies in balancing the use of strong encryption and the needs of law enforcement. Section V provides a brief summary and thus concludes the paper.
II. The Buzz
A. Software encryption used by iOS and Android
In September 2014, Apple announced its decision to change the way it would encrypt data present on its devices using Apple’s iOS, with the release of the new version of iOS – iOS8. Prior to this announcement, devices running on iOS offered encryption however the encryption only protected a small amount of the data found on the device and Apple was able to bypass the security features on the rest of the data resident on the mobile phone [2].
B. Changes to iOS and Android
The announced update to iOS8 saw the encryption of all mobile data, which is protected by a user’s passcode [3]. This essentially took any power out of the hands of Apple, that is, Apple could no longer bypass a user’s passcode and gain access to the encrypted data, thus it became pointless for law enforcement agents to request access to mobile data via wiretap orders to Apple, as had been previously done.
To compound the issue, a few days after Apple’s announcement, Google: creator of the Android operating system, which is the world’s most popular smart phone OS [4] announced their decision to follow the trend set by Apple. According to Google their latest release of the Android OS – Android 5.0: the L-release, would offer default enabled encryption; files then would only be viewable by someone entering the device password. Keys to the encryption and decryption ciphers would not be stored outside of the device by Google, so, like Apple wiretap orders served by law enforcement officials to the Tech giant for access to data on Android devices would be impossible to fulfill [4].
C. What this means for law enforcement
“Going dark” refers to the incapability of law enforcement authorities to decipher encrypted forms of communication while carrying out criminal investigation as technology continues to evolve. The announcement of updated encryption settings by Apple and Google has brought this lack of capability to the forefront.
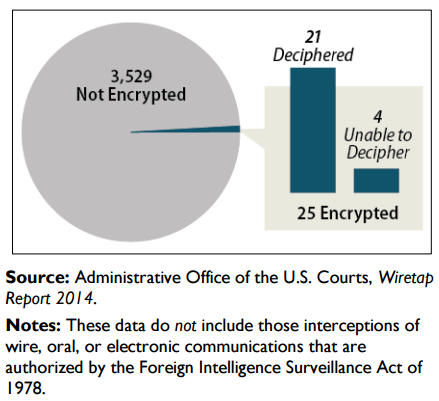
The problem is not that law enforcement agents are unable to access data but that even when data is accessed the information cannot be deciphered and so becomes unusable, frustrating the investigation process. According to testimony by [5], the Executive Director of the Science and Technology Branch of the FBI, although mobile data encryption is not new, the recent announcements by Apple and Google put a new spin on the problem: “ previously encryption had to be selected by the user now it is turned on automatically, requiring no affirmative action by the consumer ”.
Continue reading “Strengthened Mobile Data Encryption and Law Enforcement – Part 1” →